The digital landscape is evolving at an unprecedented rate, making cybersecurity a top priority for businesses, governments, and individuals alike. Among the myriad of approaches to safeguarding sensitive data and systems, the Zero Trust security model has emerged as a frontrunner in modern cybersecurity. This comprehensive article explores the principles of Zero Trust, its importance, benefits, and how organizations can implement it effectively.
What Is Zero Trust Security?
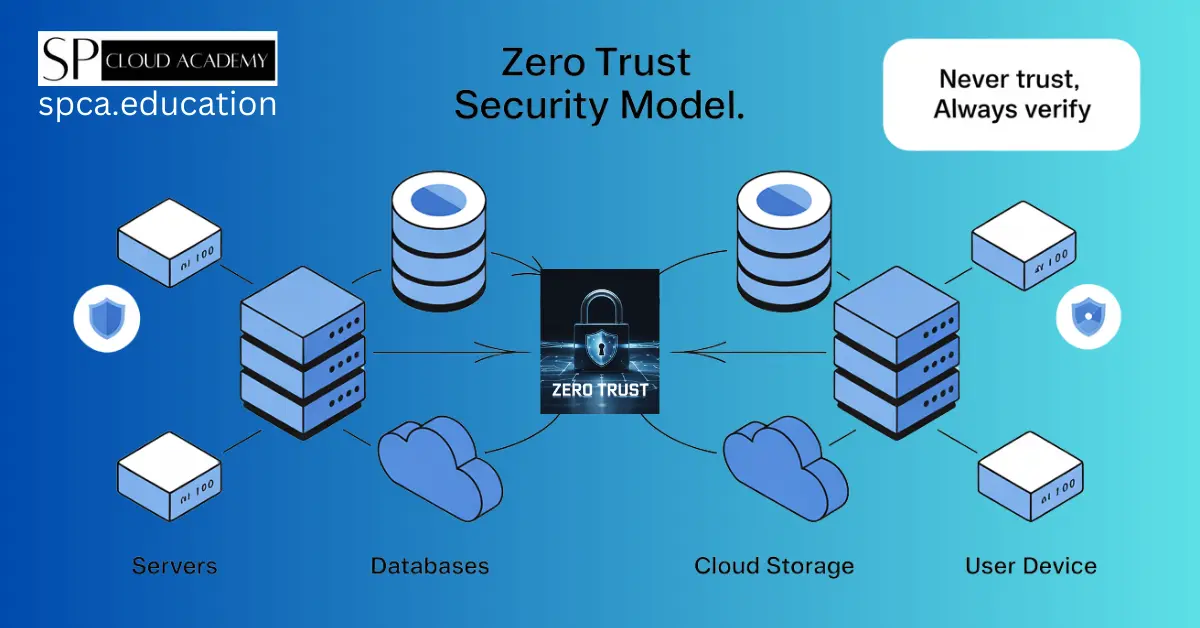
At its core, Zero Trust is a cybersecurity framework that operates on a simple yet revolutionary principle: “never trust, always verify.” Unlike traditional perimeter-based security models that assume internal networks are safe, Zero Trust treats every user, device, and application—whether inside or outside the network—as potentially untrustworthy.
This model focuses on verifying the identity and integrity of every access request, applying least privilege access policies, and continuously monitoring for threats. It emphasizes robust authentication, authorization, and encryption mechanisms to protect digital assets in an increasingly interconnected world.
The Evolution of Cybersecurity: Why Zero Trust Matters
The traditional “castle-and-moat” approach to cybersecurity, which assumes a secure perimeter and trusted internal network, is no longer sufficient. Here’s why Zero Trust has become indispensable:
- Increasing Complexity of IT Environments
- Organizations now operate in multi-cloud and hybrid environments. Employees access resources from diverse locations using various devices, making traditional security measures inadequate.
- Rise of Remote Work
- The global shift to remote work has blurred the boundaries of corporate networks, necessitating a more dynamic security approach.
- Sophisticated Cyber Threats
- Cyberattacks such as ransomware, phishing, and insider threats are more advanced, making it essential to detect and mitigate risks in real time.
- Regulatory Compliance
- Adopting Zero Trust can help organizations meet stringent compliance requirements like GDPR, HIPAA, and CCPA by protecting sensitive data and ensuring accountability.
Key Principles of Zero Trust
Zero Trust isn’t a single technology or solution—it’s a holistic approach built on several guiding principles:
- Verify Explicitly
- Always validate user identities, devices, and applications using multiple authentication layers, such as Multi-Factor Authentication (MFA) and biometrics.
- Apply Least Privilege Access
- Grant users and devices access to only the resources they need to perform their tasks, minimizing the attack surface.
- Assume Breach
- Operate as if a breach has already occurred. Continuously monitor and log all activities to detect and respond to threats swiftly.
- Context-Aware Policies
- Use contextual data such as user location, device health, and behavior analytics to make smarter access decisions.
Benefits of Zero Trust for Organizations
Implementing Zero Trust offers numerous advantages, including:
Enhanced Security
By continuously validating access requests and minimizing attack surfaces, Zero Trust significantly reduces the risk of breaches.
Greater Visibility
With real-time monitoring and advanced analytics, organizations gain deeper insights into network activities, enabling quicker threat detection and response.
Simplified Compliance
Zero Trust’s robust security framework aligns with regulatory requirements, streamlining audits and reporting.
Improved User Experience
While it may seem counterintuitive, Zero Trust can enhance user experience by enabling seamless, secure access to resources without unnecessary complexity.
Implementing Zero Trust: A Step-by-Step Guide
Transitioning to Zero Trust requires careful planning and execution. Here’s a step-by-step guide to help organizations get started:
1. Assess Your Current Security Posture
Begin with a comprehensive audit of your IT environment. Identify existing vulnerabilities, assets, and access points to determine where Zero Trust principles can be applied.
2. Define Access Policies
Establish clear policies for user and device access based on roles, responsibilities, and risk levels. Incorporate contextual factors like location, time, and device health into your policy framework.
3. Leverage Advanced Authentication Mechanisms
Implement robust authentication measures such as MFA, Single Sign-On (SSO), and biometric verification to strengthen access controls.
4. Micro-Segment Your Network
Divide your network into smaller segments, each with its own security controls. This ensures that even if one segment is breached, the attacker cannot move laterally across the network.
5. Adopt Endpoint Protection Solutions
Secure endpoints with device posture assessments, encryption, and antivirus software to prevent unauthorized access.
6. Invest in Threat Detection and Response Tools
Implement AI-powered tools and security information and event management (SIEM) systems to detect, analyze, and respond to threats in real time.
7. Educate and Train Employees
Human error remains one of the leading causes of cybersecurity incidents. Conduct regular training sessions to educate employees about phishing, password hygiene, and Zero Trust principles.
Real-World Applications of Zero Trust
To illustrate the effectiveness of Zero Trust, let’s explore its applications in various industries:
Financial Services
Financial institutions use Zero Trust to protect sensitive customer data, enable secure remote banking, and meet compliance requirements like PCI DSS.
Healthcare
Hospitals and clinics rely on Zero Trust to secure patient records, telemedicine platforms, and connected medical devices.
Government
Zero Trust helps government agencies safeguard classified information and combat state-sponsored cyberattacks.
E-Commerce
E-commerce businesses implement Zero Trust to prevent fraud, protect payment systems, and ensure a seamless shopping experience for customers.
Challenges and Considerations
While the Zero Trust model offers numerous benefits, implementing it comes with challenges:
- Cost and Complexity: Adopting Zero Trust requires significant investment in tools, training, and resources.
- Cultural Shift: Organizations need to foster a culture of security awareness to ensure successful adoption.
- Integration with Legacy Systems: Compatibility issues with outdated systems can hinder deployment.
To overcome these challenges, businesses should adopt a phased approach, prioritize high-risk areas, and seek expert guidance.
The Future of Zero Trust
As technology advances, the Zero Trust model will continue to evolve. Emerging trends include:
- AI-Powered Security: Integrating artificial intelligence to predict and prevent threats proactively.
- Zero Trust for IoT: Extending Zero Trust principles to secure connected devices in smart homes and industries.
- Quantum-Resistant Encryption: Developing encryption techniques to counteract threats posed by quantum computing.
By staying ahead of these trends, organizations can ensure robust cybersecurity in the face of emerging challenges.
Conclusion
In an era where cyber threats are ever-present, adopting a Zero Trust security model is not just a choice but a necessity. By embracing the principles of “never trust, always verify,” organizations can protect their assets, enhance user experiences, and thrive in a connected world.
Zero Trust isn’t a one-size-fits-all solution—it’s a journey. With the right strategies, tools, and mindset, businesses can successfully implement this modern cybersecurity framework and stay ahead in the digital age.
See Also
-

Incident Response vs. Disaster Recovery: The Ultimate Cybersecurity Battle Explained!
-

Data Breaches Exposed: How to Protect Your Personal and Business Information
-
Digital Forensics Explained: How Experts Uncover Hidden Evidence in Cyber Crimes
-

Ethical Hacking: The Skills, Tools, and Certifications You Need
-

The 10 Best Authenticator Apps to Secure Your Online Accounts in 2025
-

Top 10 Cybersecurity Tools You Need to Protect Your Digital Life in 2025
-

Protect Yourself Online: The Ultimate Guide to Personal Cybersecurity
-

The Ultimate Guide to Securing Your System with BitLocker, Windows Defender, and Firewall Rules
-

How McAfee Total Protection Shields You from Cyber Threats